Supply Chain Best Practices
Shops must do their part to prevent the production and sale of counterfeit products, and one aspect in their control is the security of their supply chain.
The growing problem of counterfeiting threatens businesses and consumers in nearly every region of the world. Fake products deprive legitimate businesses of revenue and undermine consumer confidence in their brand names. The damage affects both the brand, and domestic and foreign subcontractors that supply materials, components and finished products to the brand owner. Consumers are also adversely affected because they are deceived into buying fake products that don’t meet the brand owner’s standards and can pose health and safety hazards.
Governments have a particularly critical role to play in this effort. They must create the necessary legal infrastructure to protect trademarks and copyrights effectively and enforce intellectual property laws to deter fraudulent behavior. Businesses, however, also must do their part to prevent the production and sale of counterfeit products. Many aspects of the counterfeiting problem are beyond the control of businesses; however, one important area over which busi-
nesses can exert a large measure of con-trol is the security of their supply chain.
Lax security creates opportunities for counterfeit and stolen goods to make their way into legitimate production, wholesale and retail channels. Globalization, the Internet and advanced technology have made it easier for counterfeiters to infiltrate fake products into the supply chain and increase the availability of these products in markets around the world. Yet many businesses—particularly small and medium-size companies—do not fully appreciate the bottom-line cost of lax supply chain security and the adverse impact it has on brand value.
To assist businesses and raise aware-ness of the importance of supply chain
security, the Coalition Against Counter-feiting and Piracy (CACP) offers best practices that companies in a variety of industry sectors can use to improve their internal systems and coordinate with other stakeholders, including subcontractors and government authorities.
The CACP recognizes that supply chain requirements vary from industry to industry. There is not one set of best practices effective for all businesses; however, there are lessons that can be learned from businesses that take the security of their supply chains seriously.
This article provides a useful guide for businesses to assess the effectiveness of their supply chain practices and consider new options for improving performance.
The Coalition Against Counterfeiting and Piracy (CACP) is a business lead coalition led by the U.S. Chamber of Commerce. With over 225 members, the CACP seeks to strengthen U.S. and international efforts in the fight against counterfeiting and piracy.
Secure Legitimate Inputs
Companies should be vigilant to ensure that raw materials and parts are authentic and meet company standards. Increased scrutiny of exports and imports at borders is essential for policing international supply chains. The following are a variety of methods that companies should use to better police their inputs:
Ensure the authenticity of raw materials and component parts.
- Purchase materials and equipment used in manufacturing from company authorized suppliers only.
- Where possible, source from fully auditable vendors that source exclusively from original manufacturers, franchised distributors, or the first owners of the goods. - Utilize risk management procedures to identify businesses that have a high probability of engaging in trade
of counterfeit products. - Qualify vendors through periodic audits of facilities and documents.
- Consider reducing sourcing base to enhance auditing ability. - Control and audit the receipt of product ingredients and components to ensure that they meet company specifications.
Employ the concept of “strict liability” for failure to deliver authentic components and parts in contracts with suppliers.
- Include provisions in purchasing contracts to hold sellers responsible for fraudulent goods.
- Include financial penalty provisions for suppliers that fail to comply.
- Consider legal remedies if suppliers provide inferior goods.
- Develop options for rehabilitating suppliers that don’t currently use good practices.
- Develop options for delisting supplier as trusted source of raw materials and components for repeated failures to comply.
Institute shipping policies to protect the integrity of raw materials and component parts.
- Develop guidelines to ensure the physical security of overseas factories in the supply chain (e.g., like those for the U.S. Customs-Trade Partnership Against Terrorism/C-TPAT).
- Use seals on all containers and note seal numbers on shipping manifests to protect containers from being opened and resealed.
- Fully inspect carrier documents.
- Develop partnerships with customs authorities to exchange information and target shipments suspected of containing counterfeit products.
Verify Legitimacy of Customers and Distributors
Counterfeiters prey on weaknesses in the legitimate supply chain. Often they pose as legitimate businesses and seek to purchase products in bulk in order to blend fake products and maximize returns and launder resources. Manufacturers should be vigilant in ensuring that they only sell to legitimate distributors or retailer outfits. The following are some best practices businesses should use to verify the legitimacy of customers and distributors:
Utilize risk management procedures to verify legitimacy of customers.
- Develop guidance for the sales force on how to assess the legitimacy of customers.
- Has the customer ordered an unusually large volume for normal needs?
- Is the customer willing to pay cash for very expensive orders?
- Does the customer have an appropriate business background?
- Do the product capabilities fit the customer’s line of business?
- What do financial institutions say about the company’s credit?
- Are delivery dates vague or are deliveries planned for out-of-the-way destinations? - Educate and train the sales force on guidelines. Develop incentives and penalties for adherence to guidelines.
- Employ investigators to track customer history and refuse to do business with organizations that have been found to
trade in counterfeit goods.
Ensure that subcontractors only produce authorized merchandise.
- Perform audits to make certain that subcontractors are not running “third shifts” to replicate product for distribution in the illegitimate market.
- Delist suppliers that routinely produce surplus supply.
Manage Production Waste and Damaged or Unusable Inventory
Individuals engaged in counterfeit trade often prey on scrap yards, waste repositories, or reclamation centers to obtain inferior goods. Companies have employed the following policies to deter theft and diversion of these goods:
- Institute policies to certify that production waste, and damaged and unusable products are destroyed or appropriately disposed of.
- Select one or two trusted charities for product donation to ensure that goods are not diverted to the gray market and blended back into the legitimate supply chain.
Ensure Legitimacy of Purchased Products at Retail Level
Retailers employ a variety of tools to ensure the legitimacy of purchased products. The following are some of the methods they use:
Verifying product authenticity.
- Audit shipments from all sources (especially those that do not come directly from manufacturers) to verify authenticity of packaging, case markings, pallet configurations, etc.
- Open product cases to confirm that units have the same batch numbers, expiration dates and uniform product
codes (UPC). - Employ track and trace methodologies with bar codes or RFID.
- Audit products on the shelves for consistency of packaging, quality and freshness.
Authenticating distribution partners.
- Institute procedures for authenticating distribution partners and ensuring their legitimacy.
- Establish through contract provisions the requirement that products be original and unadulterated.
- Products must be in manufacturer cartons, cases or shippers.
- Repackaged or recycled materials should raise suspicion.
- Original carton case seals (or unit packaged when totes are used) must be sealed and unaltered.
Monitor Brand Integrity
It is incumbent upon rights holders to monitor the retail space and report intellectual property infringements. Brand owners employ a variety of strategies to enhance protection for products and to route out fakes in the system.
Collaborate with local customs authorities.
- Register trademarks with customs authorities. Provide samples of legitimate products and train authorities and law enforcement to recognize contraband.
- Provide information about “bad actors” with local customs authorities so that they can increase scrutiny of shipments from particular facilities or importers.
- Develop procedures with customs authorities to permit sharing of information on the source of counterfeit products seized and the names of businesses and individuals involved.
Enhance market intelligence.
- Utilize “mystery shopping” techniques to gather random samples of products and monitor the marketplace environment.
- Test and certify product authenticity.
- Use results to tailor necessary action plan.
Monitor sales of brand name products on the Internet.
- Monitor Internet auction sites carefully and pursue appropriate legal remedies if necessary.
- Employ tactics such as mystery buys to verify authenticity of products sold on the Internet.
Consider using technology to ensure product security.
- Examine options for applying simple, low-cost solutions that could help differentiate authentic products from counterfeit products.
- Examples of low-cost options include deliberate packaging flaws and covert product design flaws. - Consider the applicability of new technologies that offer more technically advanced features. Examples include:
- Bar code symbologies, such as Reduced Space Symbology (RSS) and other globally recognized 2-D composite symbologies.
- Radio Frequency Identification (RFID) tags.
- Holograms and watermarks.
- Anti-counterfeiting printing ink technologies.
- Covert features on products.
Vigorously pursue legal remedies to deter trademark infringements.
- Employ litigation strategy to deter future infringements.
- Seek out additional information about suppliers through legal process (e.g., the “discovery” process
in U.S. courts).
- Consider taking legal action, evenn on small counterfeiting cases, to demonstrate to those engaged in counterfeiting activities that they are at risk no matter what the level of sales activity.
- Utilize Ex Parte Temporary Restraining Orders, Orders of Seizure, and Asset Seizures where possible.
- Use creative civil enforcement efforts such as Facility/Venue permanent Injunctions and Orders of Seizure; National Preliminary Injunctions and Orders of Seizure; suits against Secondary Infringers (contributory and vicarious liability) such as services, financiers and landlords.
Partner with retailers.
- In areas where there is a high degree of counterfeiting, consider adopting certified retailer programs.
- Work on a signpost or slogan for consumers to guarantee authenticity of products (e.g., “No trade in fakes”).
Outreach to Law Enforcement and Regulatory Officials
Businesses can reap big dividends from a strong outreach program to educate federal, state and local law enforcement as well as regulatory officials and support their efforts to enforce laws against fraudulent activities. Law enforcement officials, in particular, need industry help in understanding how counterfeiters and their accomplices carry out illegal activities and what the impact is on business, consumers and law enforcement priorities (e.g., collecting tax revenue; fighting organized crime; and enforcing consumer health, safety and environmental regulations). Some also will appreciate the opportunity to share information that will help them in their enforcement work.
Possible initiatives include:
- Develop informational materials that explain the harm that counterfeit products cause businesses, consumers and governments—giving specific examples and providing economic data and statistics.
- Meet with key federal, state and local officials and customs authorities to personally brief them and learn more about their priorities. Help them understand legitimate distribution channels in an industry and how counterfeiters abuse this system.
- Establish procedures for sharing information that can be used in law enforcement investigations and offer to
provide legitimate products, under appropriate conditions, to assist in investigations. - Provide a counterfeit product destruction service to ensure that seized counterfeit products are properly disposed of.
- Monitor court dockets on counterfeiting cases to gauge enforcement trends and improve outreach efforts.
Conclusion
This information serves as a resource to businesses in their fight against counterfeiting and piracy.
Related Content
ICYMI--MMT Chats: What's Happening to Our Industry? Time to Take a Stand for Plastics
MoldMaking Technology Editorial Director Christina Fuges chats with Bob Schiavone, Global Marketing Director for R&D/Leverage about his passion for manufacturing, marketing and the mission to change the perception of plastics. This episode is brought to you by ISCAR with New Ideas for Machining Intelligently.
Read MoreMMT Chats: Marketing’s Impact on Mold Manufacturing
Kelly Kasner, Director of Sales and Marketing for Michiana Global Mold (MGM) talks about the benefits her marketing and advertising, MGM’s China partnership and the next-generation skills gap. This episode is brought to you by ISCAR with New Ideas for Machining Intelligently.
Read MoreMMT Chats: Impressions and Inspirations from AMBA Event that “Shifts the View”
MoldMaking Technology Editorial Director and Managing Editor share their takeaways from a recent American Mold Builders Association Conference focused on leadership and mentorship in the moldmaking community. This episode is brought to you by ISCAR with New Ideas for Machining Intelligently.
Read MoreMMT Chats: Simple Steps to Get Your Social Media Campaign Started
MoldMaking Technology Editorial Director Christina Fuges catches up with Gail Now’s Chief Curiosity Officer Gail Robertson. We talk about the importance of using the curiosity tool to tell your stories as part of a marketing strategy that includes social media. This episode is brought to you by ISCAR with New Ideas for Machining Intelligently.
Read MoreRead Next
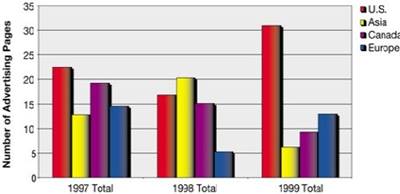
Growth Strategies for the U.S. Moldmaker - Understanding Your Competition - Here and Abroad
This article begins a four part series that will describe the current competitive conditions in the plastics tooling industry and what some companies are doing to grow their businesses amidst challenging conditions.
Read MoreReasons to Use Fiber Lasers for Mold Cleaning
Fiber lasers offer a simplicity, speed, control and portability, minimizing mold cleaning risks.
Read More






_300x250 3.png;maxWidth=300;quality=90)


.png;maxWidth=300;quality=90)





.jpg;maxWidth=300;quality=90)