Manufacturing cyberattacks are expensive, hard to detect and dangerous. Companies can no longer sit idle and hope not to be a target. Hackers are stealing everything from personal information to internal operational details and intellectual property. A single data breach can cost a manufacturer a year’s worth of proprietary information and lead to a permanent loss of customer trust. The damage to a company’s reputation is practically unfixable.
The challenge for manufacturers is as supply chains, operations and facilities get more connected, the risk is more significant and far-reaching. The added challenge for small and medium shops is combining legacy equipment with modern technology, which adds to the security gap in many facilities. The final major hurdle is the modern technology itself. IoT devices were never designed to protect themselves from threats. Since robotic arms are not compatible with firewalls, for example, hackers are exposing those weaknesses. These facts make any shop a highly enticing payday for criminals.
What the Hack Is Going On?
Security researchers and analysts have raised questions about the manufacturing industry's preparedness to deal with cyberattacks. For example, Vectra, a company dedicated to enterprise-wide cyberattack detection, released its 2018 Black Hat Edition of the Attacker Behavior Industry Report this past summer, which provides insight into methods and types of attacks the manufacturing industry is facing. The key findings reveal that attackers who evade perimeter security can easily spy, spread, manipulate, and steal, unhindered by weak internal access controls.
The report also shows a significant increase in malicious internal behaviors, such as when someone with access to a network deliberately sabotages work, which is a reliable indicator that attackers are already inside the network. Typically that is an employee or disgruntled employee working to harm a company's product(s) and reputation. On top of that increase, the report describes an unusually high volume of reconnaissance behaviors, such as when a hacker gets into a network and looks for anything of value to steal like models, intellectual property, shop operations or equipment. Hackers know that once they gain access to a manufacturing network, they can come in often because of the lack of cybersecurity. Reconnaissance behaviors are a reliable indicator that attackers are mapping out manufacturing networks in search of critical assets. Although this report paints a bleak picture for manufacturing today, the real challenge is how to better protect what companies are building for tomorrow.
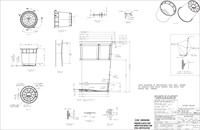
For example, an attack on the supply chain is one of the worst-case scenarios as it will taint products or services at the time of their creation. However, what if criminals take it a step further? Another cybercrime scenario for engineers and manufacturers is the deliberate manipulation of design models and shop equipment, which are next to impossible to detect.
Those microvariations result in a real change that could make a part less efficient, shops unsafe and put lives in danger. Companies should consider any connected device on the shop floor at risk.
And, if you are designing parts that are mission-critical, the size of your company does not matter. You have to take cybersecurity measures, or else you take a big risk of failure.
Cybercrime software is the second layer of cybersecurity. The journey starts with people. It is essential for employees to be aware of best practices because they run operations, machines, and other manufacturing assets.
Strategies for the Shop
An example of a cybersecurity tool to help protect your company is Physna software, which is used as a standalone or plugin for CAD software. When a user saves a file, data is analyzed and stored separately within Physna. When the user reopens the file, a quick check ensures no manipulation has taken place. If detected, the software displays the change, shows the data and a 3D representation of the exact change.
This cybercrime tool was initially designed to protect intellectual property because of the growing cybercrime problem. Physna, short for "Physical DNA," uses a series of advanced algorithms and artificial intelligence to break down and analyze models, their features, patterns, relationships, and any similarities and differences between 3D models.
This software is the second layer of cybersecurity. The journey starts with people. It is essential for employees to be aware of best practices because they run operations, machines, and other manufacturing assets.
A small- to mid-size manufacturer must act as a human firewall, implement secure communication methods, develop a sophisticated password strategy, use a secure backup plan, be aware of the internal threats, educate employees and promote vigilance to protect their company data.
Here are three top strategies:
- Develop and share best practices with employees, partners, and customers. Anyone a company does business with can become a potential cyberthreat. Companies need to be direct and make sure vendors, suppliers and partners are aware of those best practices. There are plenty of data breach examples where hackers stole the data through a third-party vendor, gaining access to millions of people. Begin your best-practices policy by securing communication methods.
- Fortify your firewalls. Firewalls are not enough. Shops should encrypt systems with anti-virus software. Shops should also incorporate sophisticated password strategies and install all security updates.
- Monitor and record all activity. Constantly monitoring shop systems is a proactive security strategy that actuates real-time detection. If hackers get into your company’s systems, you have to be able to identify it first. The next challenge is to repair the damage and fix the vulnerability.
Detection is key. If program files do not match the program running the device, the shop must detect the mismatch, identify the deviations and alert the appropriate people. Do not assume your software will do it on its own.
Good record-keeping of incidents, alerts, and advisories will help determine the true impact of the security policies in place. Lastly, protect your models. They are vulnerable to theft as well as manipulation. Back up and secure them in a central storage space. Being prepared will help undo unauthorized or malicious changes.
While cyberexperts have been protecting companies with vigilance, better password management, and better employee education, companies are also working to make better tools to stop a cyberattack before it starts.
For More Information
About the Author
Paul Powers is CEO of Physna, a software company working with manufacturers on automation, quality control, and inspection.
Related Content
Leading Mold Manufacturers Share Best Practices for Improving Efficiency
Precise Tooling Solutions, X-Cell Tool and Mold, M&M Tool and Mold, Ameritech Die & Mold, and Cavalier Tool & Manufacturing, sit down for a fast-paced Q&A focused on strategies for improving efficiencies across their operations.
Read MoreOEE Monitoring System Addresses Root Cause of Machine Downtime
Unique sensor and patent-pending algorithm of the Amper machine analytics system measures current draw to quickly and inexpensively inform manufacturers which machines are down and why.
Read MoreThe Trifecta of Competitive Toolmaking
Process, technology and people form the foundations of the business philosophy in place at Eifel Mold & Engineering.
Read MoreFrom Injection Mold Venting to Runnerless Micro Molds: MMT's Top-Viewed June Content
The MoldMaking Technology team has compiled a list of the top-viewed June content based on analytics. This month, we covered an array of topics including injection mold venting, business strategies and runnerless micro molds. Take a look at what you might have missed!
Read MoreRead Next
How to Use Strategic Planning Tools, Data to Manage the Human Side of Business
Q&A with Marion Wells, MMT EAB member and founder of Human Asset Management.
Read MoreReasons to Use Fiber Lasers for Mold Cleaning
Fiber lasers offer a simplicity, speed, control and portability, minimizing mold cleaning risks.
Read MoreHow to Use Continuing Education to Remain Competitive in Moldmaking
Continued training helps moldmakers make tooling decisions and properly use the latest cutting tool to efficiently machine high-quality molds.
Read More








.jpg;maxWidth=300;quality=90)








_300x250 3.png;maxWidth=300;quality=90)











