Establishing a Cyber-Secure Moldmaking Operation
Appears in Print as: 'Establishing a Cyber-Secure Moldmaking Operation'
Mold builders must understand subnetwork setup, threat and risk analysis, and support structures to protect its data.
#Basics #FAQ #analysis
The integration of information technology (IT) for data-centric computing with operational technology for monitoring and adjusting events, processes and devices throughout a mold shop presents cybersecurity concerns. However, many mold shops today still do not take any measures to secure their data, despite all the intellectual property (IP) represented in the manufacturing and simulation data a mold builder uses to design and manufacture tooling. Here is a recommended path a mold builder should follow to address cybersecurity properly.
A mold builder should first properly plan its network infrastructure, determine the components to hook up and identify the locations that require perimeter security. Networks are incredibly quick and easy to set up, but without proper planning, so-called "flat networks" are created that give equal permission to all components that comprise the network.
Featured Content
Every piece of equipment communicates with every other piece of equipment, and all internal devices are routed to an outside network, such as the internet. So, it is important that devices inside the network with different levels of criticality are isolated from one another, called the least privilege principle. This principle means that if this type of communication is not necessary for the benign operation of the shop, then it should not even be possible. For example, when integrating a Wi-Fi radio into the network, there is no need for that radio to communicate with a CNC machine.
A solution is to design logically separate subnets (subnetworks) — a logical partition of an IP network into multiple, smaller network segments — that are isolated using firewall equipment.
A mold builder should first properly plan its network infrastructure, determine the components to hook up and identify the locations that require perimeter security.
Setting Up Subnets
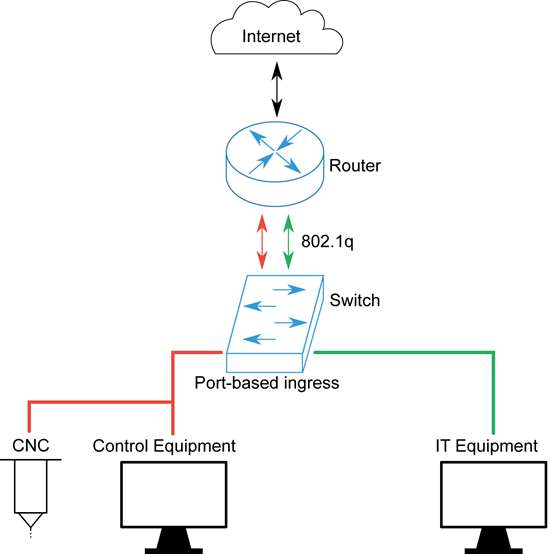
The network diagram in Figure 1 depicts a two-zone configuration in a mold shop. One zone contains a CNC router and a control computer, and the other zone contains typical IT equipment, such as an office PC. A shop should isolate both zones from each other and assign different privileges when routing outside of the local network into the internet. The challenge with this configuration is that it isn't feasible to physically separate all networks from each other.
One solution is to use virtual LAN (VLAN)-capable switches and routers, which almost all business equipment has, but people often ignore. These switches and routers allow shops to create virtual local area networks (LANs) — or a group of computers and associated devices that share a common communications line or wireless link to a server — inside the LAN that are isolated on the switch on the data link layer. Basically, this means that all traffic that is entering on the switch of the red subnet is entirely separate from the traffic on the green subnet.
A shop does not need to have the same number of cables as it has VLANs when passing that data on to another network device like a router. Instead, the shop can utilize a feature called 802.1q VLAN tagging, in which every packet has a digital ID tag. The final destination, such as the router, can then distinguish the original physical source subnet of every given packet and make an informed routing decision.
The configuration can include full internet routing for the green subnet, but only allow access to the CNC machine vendor's firmware update site for the red subnet. With such technology, the shop can efficiently and easily manage hundreds of completely separate subnets. The shop can also follow the defense in depth security principle, which means that if a piece of equipment is compromised the shop can retain control over all other parts of the network. For example, if an employee accidentally downloads malware on an office PC, the shop must ensure that the infection is contained to only a subset of the whole network and not allowed to infect other components.
One solution is to use virtual LAN (VLAN)-capable switches and routers, which almost all business equipment has, but people often ignore.
Analyzing Risk
Proper planning of a shop network not only includes verifying the secure installation and documentation of components inside that network but also a look at all the assets from an attacker's point of view. This is what is commonly known as a threat and risk analysis, through which a shop lists the threats that apply to the network analytically, describes and implements the countermeasures and describes the potential worst-case scenario in case of a breach.
A worst-case scenario can range from the outage of one machine to the outage of a whole production line or the outright physical damage of machines. Another example is an attacker who gains access to some of the CAM sources, through which they can steal valuable IP or subtly change the given CAM programs, yielding a mold that appears correct, but in reality, does not match the specifications anymore and requires expensive re-production.
Someone familiar with the estimation of security levels can estimate the level of residual risk that is acceptable in the context of the particular mold shop. For example, they would analyze the assets and the number of separate zones they should maintain. This information would then be used by an IT professional to configure the network equipment to perform its function as it is laid out in the risk and threat analysis blueprint.
Proper planning of a shop network not only includes verifying the secure installation and documentation of components inside that network but also a look at all the assets from an attacker's point of view.
Applying Best Practices
Finally, the components that are networked with each other play a vital role in the security of all networking. After all, the best network isolation and planning does not matter if the machines themselves are vulnerable to attacks, regardless of their configuration.
Mold shop ownership must determine what precautions to take for a particular machine and how the vendor will ensure the continued security of a given system. For example, the time period for firmware updates containing security patches and a penetration test of a machine's communication equipment. However, some of the responsibility of keeping good cyber hygiene also lies with the mold shop. For example, ownership must know if their machines are configured according to hardening guides that the vendor provided, if secure authentication is used for all types of equipment and if the interfaces the shop is not using are correctly disabled.
One critical part of the infrastructure is the VLAN-capable switch, which is also configurable over the network itself. This switch must be configured so that in its final state, all reconfiguration access from either the red or green network is entirely disabled. This will ensure that an attack cannot simply circumvent security controls by reconfiguration of the networking equipment. It also requires an attacker to be physically present at the switch to make any changes and, even then, there would be a unique password to make such changes.
Getting Proper Support
While some of these points are straightforward to implement, others such as penetration testing, might not be familiar to someone who is not doing security work on a routine basis. Fortunately, the proper support is available from trusted external suppliers who can help anything from planning new equipment purchases to analyzing and verifying existing equipment with preexisting cybersecurity measures.
About the Author
Author Name
Dr. Johannes Bauer works as a Principal Security Advisor at UL.
RELATED CONTENT
-
Why Choose a Valve-Gated Hot Runner?
Moldmakers need to be aware of how different gating technology can affect their customers when designing a hot runner system into a mold.
-
How to Deal with Graphite Dust, Part 1
A review of the characteristics and considerations when handling graphite dust.
-
7 Key Advantages of Hot Runner Systems
While both hot runner and cold runner systems have their benefits, for design flexibility as well as reduced cycle times and costs, hot runner systems will probably be the better choice.